Hamburg – just about one year ago, the first BSides was organized by Arron and Caroline. Now, one year later on 28th December, just after a relaxed Christmas time, they invited again – for the next #BSidesHH. It was powered by the great location at the University of Hamburg as well as by more attendees compared to last year – yay, we got the 100! Although I had not enough time to attend the 32C3 this year, I had to take the opportunity to attend the BSides, and it was really worth the time (again)! So here’s a small summary of the talks, I was listening to, but it was not only about these talks, but more about really nice people coming together to enjoy some free mate and pizza. I know that I’m just repeating myself from what I have said last year, but Arron and Caroline – thank you very much for an awesome conference!
So the BSidesHH was kicked off by Meredith Patterson with her talk “Ambiguity Is Insecurity“. She compared security vulnerabilities to language theory, where for example simple and shortened sentences like “Oh, look there!” can be interpreted by the receiver of the message in a completely different way, like “Oh, look there is a nice bar!”, although the intended meaning of the sender could be “Oh, look there the train is arriving”. In software this could be applied too, because applications may interpret input in different ways, although the intended meaning is completely different. This is due to the fact that software mostly expects input in a predefined way, which could be messed up by submitting seemingly incomplete or false input. The resume: Security vulnerabilities are the result of ambiguity, so let’s built more secure programming languages! You should listen to this talk as soon as the video material is uploaded!
Another non-technical talk “State-Surveillance: Treason, Heresy and the Boy That Drives The Plow.” held by Arron Finnon himself, which was quite similar to his last year’s talk. He introduced some very interesting previous historical events, which can be directly compared to at least some kind of surveillance, how we’ll recognize it today mainly through the NSA. And by “previous” I do not mean “previous”, but rather “really long ago”. The statement “State-Surveillance is older than any state denying it’s involvement in it” perfectly fits as forms of surveillance can be found hundreds of years ago – in the time of Martin Luther and even longer ago. Arron’s talk showed that even this kind of talks can be extremely interesting when presented the right way! If you have missed his last year talk about historical events connected to security, revert back and have a look at both!
After having lunch with some free, sponsored pizza, a more technical talk “Testing SSL” by Dirk Wetter, the author of the infamous testssl.sh script, was held about its development, current status and upcoming features. Since every penetration tester probably came across this tool once in his or her life, it was quite interesting to get to know something about its internals. Just use it – it’s pretty smart!
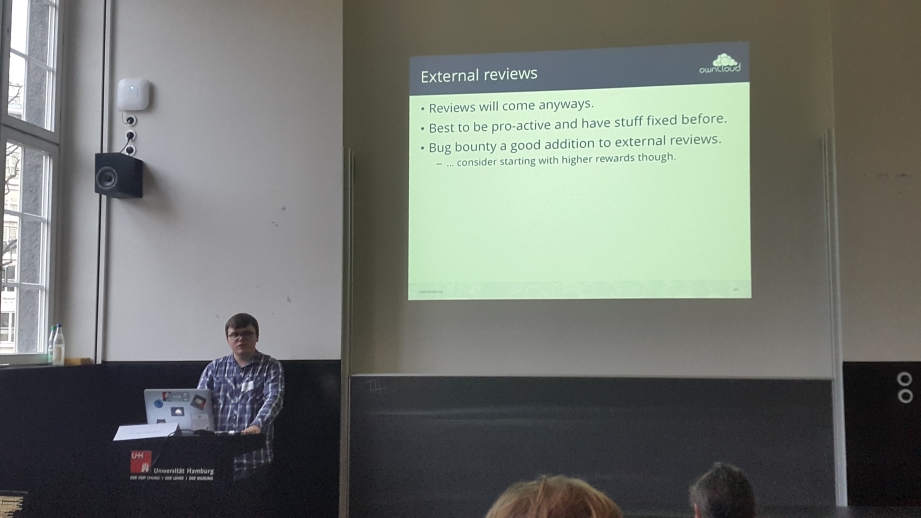
In my opinion the most interesting talk of the day started right afterwards: “Ramping up Security at an open-source startup: Lessons learned.“. Lukas Reschke, lead of security at ownCloud presented some very interesting insights about the security works on the ownCloud project. Although there’s a lot of hate going on in regards to this cool project, the talk clearly showed that – especially after introducing the HackerOne bug bounty program and in addition to internal code reviews, more and more bugs get killed to strengthen this project used by major players. It was also interesting to hear something about the operator side of a HackerOne program, rather than only the hunter side. Great insights!
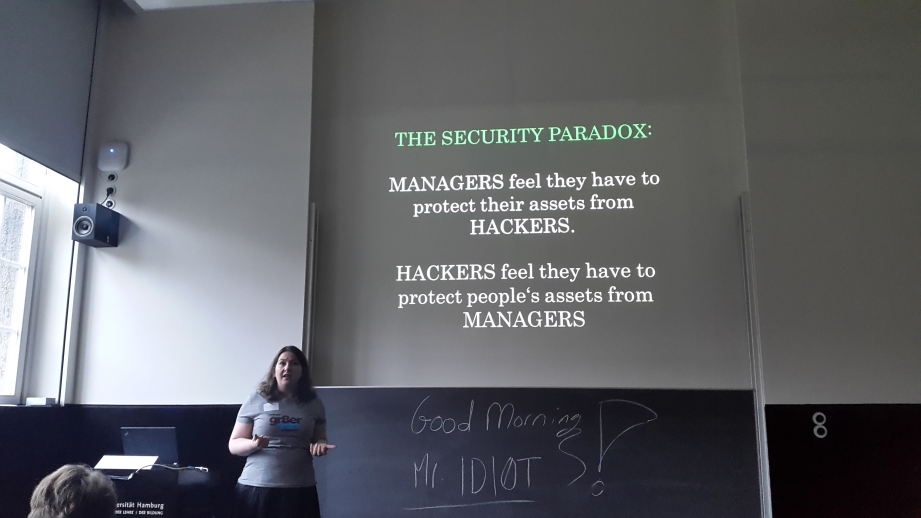
I really enjoyed Caroline Krohn’s last year talk about crazy managers (well, they are still crazy 😉 ), and in her talk “Ignoring Hackers, hunting Hackers, fearing Hackers.” she discussed the gap between managers and hackers. In fact most managers seem still to fear hackers – even in a way, that they don’t want to get listed on her own website, because they fear getting hacked then, just because Caroline connects with hackers. On the other hand, hackers try to “protect people’s assets from managers” in form of vulnerability disclosures. I think Caroline does a really good job in convincing managers of the contrary!
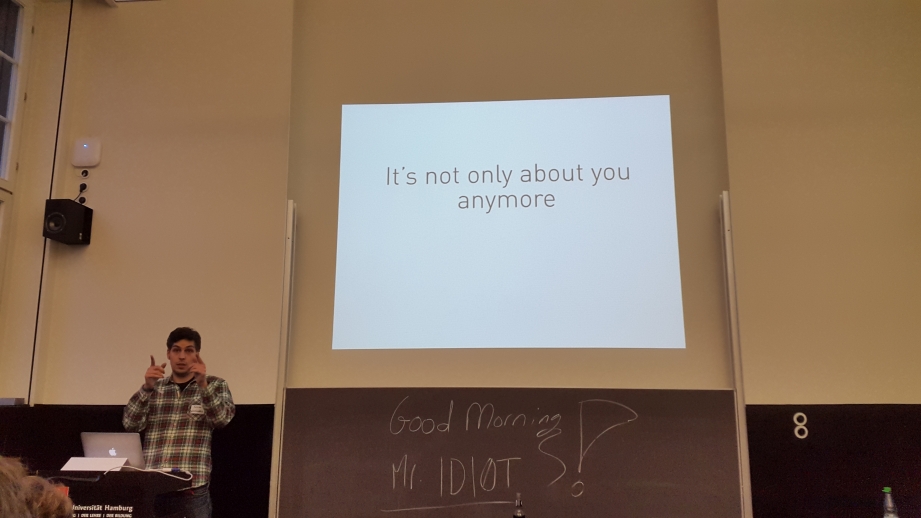
The talk closely connected to Caroline’s “It is not only about “you” anymore!” by Fabian Koch showed that it is necessarily important to talk to “normal”, non-technical folks about security issues in a simple and figurative way to raise awareness and make things understandable. Totally agree – show them shodan.io!
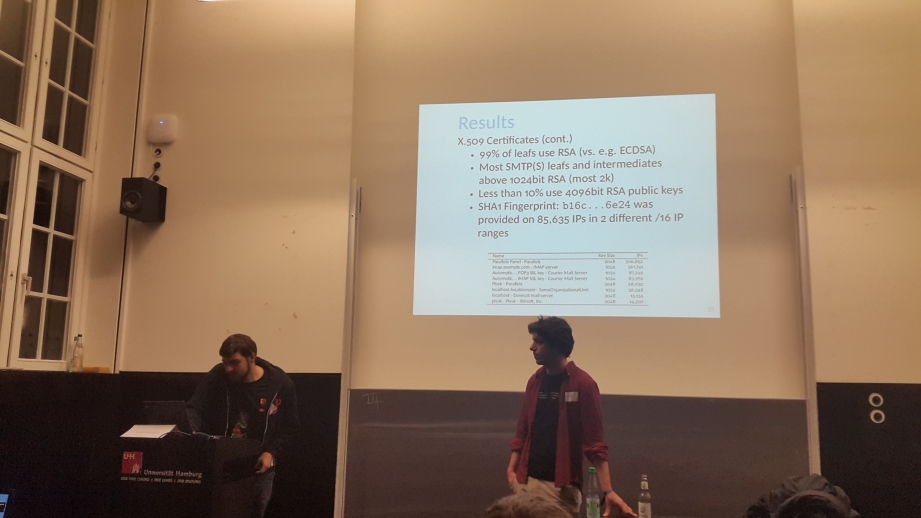
The last talk of the day “Yep! We poked all your mail daemons. State of Transport Security in the E-Mail Ecosystem at Large” was also a quite interesting one! Aaron Zauner and Wilfried Mayer masscanned the whole internet for mail-servers and analysed their security related settings and presented their findings. This covers not only the enabled SSL/TLS versions on the scanned servers, but also used algorithms and even used certificate fingerprints – btw. interesting to see, that the same SHA1 certificate fingerprint is presented on ~85.000 different IPs in two different /16 networks. So what’s going on there? Is it China 😉 ?
By the end of the day, the whole conference was a real success – not only due to interesting talks and awesome folks, but rather due to the perfect organization!

And to close this post, it looks like two major nations have been attending the conference too 😉


